Compliance with HIPAA is not the same thing as security. The enforcement model is largely complaint-driven, which means an organization can be out of compliance for months or years and not know it until something goes wrong. There are also other regulations governing data security, such as PCI DSS for payment data, state privacy laws, and sector-specific requirements that HIPAA compliance alone does not satisfy.
HITRUST CSF is the next step beyond HIPAA.
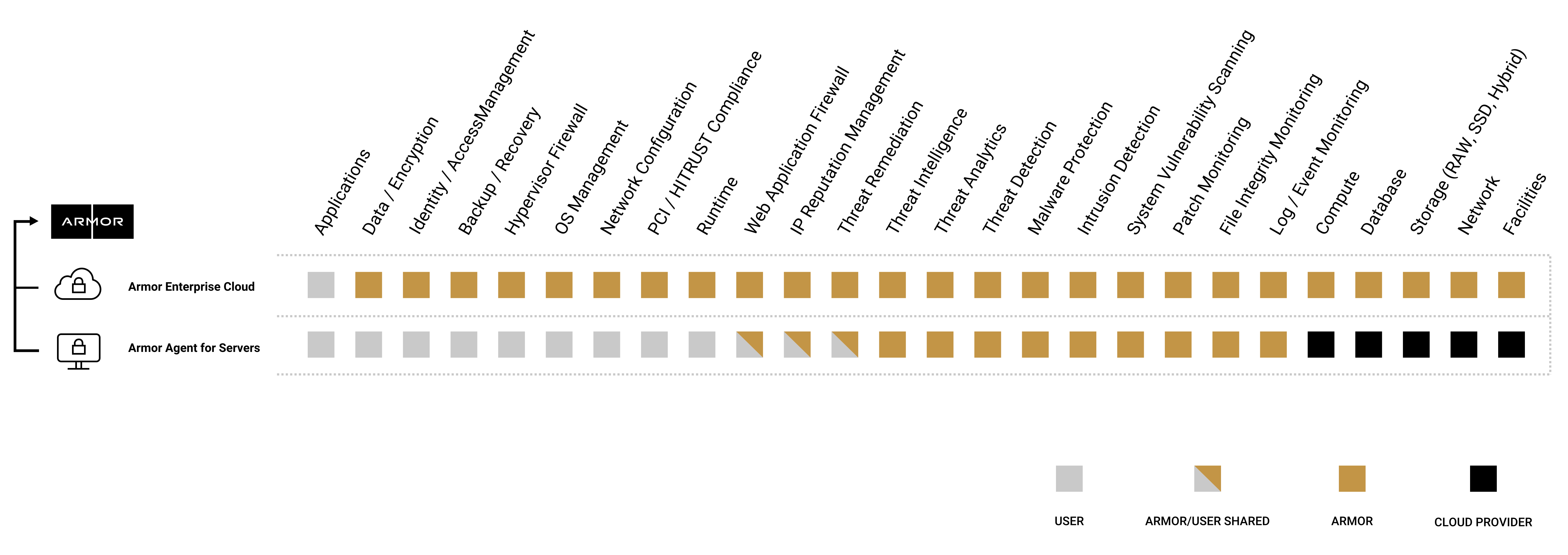
HITRUST maps controls across HIPAA, NIST, ISO, PCI, and others into a single audited framework. Certification requires third-party validation against hundreds of specific controls and re-validation on a defined cadence. A HITRUST CSF–certified provider has been inspected in detail.
For organizations that need a higher and verifiable security bar, or that need to demonstrate that bar to customers, partners, or regulators, HITRUST is the next step beyond HIPAA. We’ve covered the specifics of HITRUST certification in a separate piece.
Armor is HITRUST CSF certified. We’ve also helped many of our customers achieve their own HITRUST certification.
Whether you stop at HIPAA or pursue HITRUST, the point is the same. Protecting PHI is what’s required of you, and the consequences of failing are real. Fines have grown more aggressive since the HITECH Act, and a breach affecting PHI is one of the most expensive incident categories in any industry, with healthcare leading for 14 consecutive years.