Through smart integrations of electronics, sensors and connectivity, the internet of things (IoT) has enabled us to automate an increasing number of day-to-day tasks. On the flip side, it’s also bringing in new threats. In fact, it didn’t take much time for IoT devices to be responsible for some of the largest DDoS attacks in history. In this post, we discuss various aspects of IoT and expose the good, bad and ugly sides of what’s inevitably becoming a permanent fixture of our lives.
What exactly is IoT?
IoT refers to the physical objects growing ever more present in our households and workplaces that have a means to communicate with other devices across some form of network, most commonly through WiFi or Bluetooth. This definition for the Internet of Things could be further expanded to include anything with an IP address. So, while we often associate IoT with ‘smart’ anything, it could also mean our desktops, laptops, servers, routers, proxies, etc.
A brief look at IoT history
In order to understand how we got to a point where even refrigerators and pets are getting internet connectivity, let’s take a quick look back at the past. If we all agree that anything on the network can be considered an IoT device, then we’ve had IoT (albeit in a very limited and much more physically defined form) since at least 1969, when the first ARPANET link went live.
At that point, network access was severely limited to certain geographical locations. if you weren’t physically able to connect a device to the network, then there was no access. But this also meant that network security wasn’t really a major concern, as the hosts and endpoints of those very limited networks were typically found in inherently secure places (i.e. government-owned premises and academic campuses).
In the early days, the Internet was only meant for research and academic purposes. But as Internet adoption grew, so too did the number of people who could access it. Fortunately (and unfortunately) these new entrants also brought with them new thoughts and ideas on how the network could be used, and for some – abused. When maliciously creative individuals finally found a way to abuse the connected devices for their own amusement, the first malware was born.
Because the original designers of the Internet were focused on building an infrastructure for only a handful of purposes, they failed to foresee the threats we now face as the complexity and connectivity of the Internet has grown. Most of the security issues that exist today can be traced to that unwitting decision in the past of leaving security as an afterthought.
Although the growth of the Internet and the things depending on it has been largely exponential, the sudden explosion of modern-day IoT devices can be attributed to two technological advancements: Cellular in 1973 and WiFi in 1991.
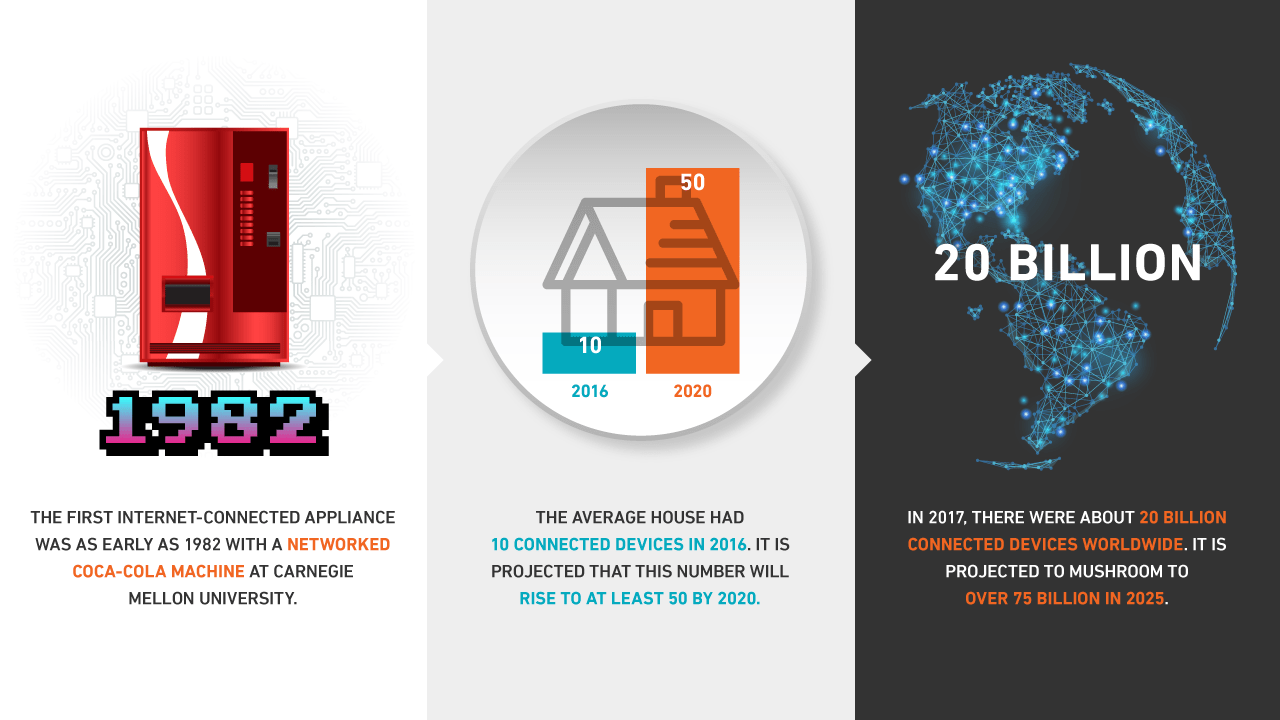
Today’s IoT devices can trace their immediate origins to as early as 1982, when a networked Coca-Cola machine at Carnegie Mellon University became the first internet-connected appliance; ultimately leading to the smart-fridges of today.
However, there’s a slight difference in how consumers and businesses perceive IoT. Consumers tend to think in terms of gadgets and ‘smart’ things; e.g., smart speakers, smart watches, smart dog collars, or just about any small gizmo that allows them to control or monitor some aspect of their environment.
Businesses, on the other hand, usually group IoT into two buckets:
- IoT devices employees and/or customers introduce into the corporate network (commonly handled by BYOD policies) and
- IoT devices that enable business functions. These types of devices are numerous and include things like networked manufacturing equipment, sensor-equipped wind turbines (that work to optimize efficiency), or the currently evolving class of autonomous vehicles that perform car-to-car and car-to-infrastructure communications.
All these innovations and the tasks they perform make up the ‘good’ side of IoT. Regardless of the type of IoT (consumer-based or business-based), an overwhelming majority of these devices are still built with security as an afterthought, rather than by design. This is what’s causing the bad and ugly sides of IoT.
Security concerns of IoT
From a security perspective, the main issue with IoT devices boils down to three factors: exploitability, prevalence, and lack of support.
Exploitability
Unfortunately, the majority of IoT devices are rolled out with grossly exploitable vulnerabilities. For example, the Mirai botnet, which was responsible for a couple of record-setting DDoS attacks, was able to ensnare IoT devices by simply taking advantage of factory default usernames and passwords that were left unchanged.
Like smart devices, server applications and other network devices come with default login credentials upon installation. Because these assets are usually deployed in a corporate environment, security-conscious system administrators change these credentials before deploying them into production environments. Unfortunately, consumer-based IoT devices that are brought into households and small offices aren’t subjected to these risk-mitigating practices.
Some of these devices even have components that aren’t protected by a password. In fact, last year, a consumer group called for the recall of certain connected/intelligent toys whose Bluetooth connections weren’t password-protected. The vulnerability made it possible for attackers to download the toy’s corresponding app and then communicate with kids who owned these toys through the toy’s speech feature.
Prevalence
In 2017, there were about 20 billion connected devices worldwide. That number is projected to mushroom to over 75 billion in 2025. There’s no question about it – IoT devices are already and still increasingly becoming more and more prevalent. This ubiquity, coupled with their connectivity capabilities, make these devices prime targets for different forms of abuse.
The massive DDoS attacks that were launched from an IoT botnet mentioned earlier is just one example. Imagine if attackers could take control of power and life support systems (presumably running IoT devices) on a grand scale and then demand a ransom using ransomware.
Lack of support
It is thankfully becoming the norm for IoT devices to receive security updates. One major caveat is that many devices are created to last more than a decade, but most manufacturers release multiple devices per year. This means the financial motivation to spend resources maintaining 10-year old code is practically non-existent, considering that businesses need developers working on the latest product.
How developers/manufacturers can mend the bad and ugly side of IoT
Solving the security conundrum facing IoT developers/manufacturers isn’t as simple as it sounds. If it was, it would have already been done. A general solution to the problem would probably involve most of the following:
- Make device security a priority during the development process;
- Isolate software components that don’t need to communicate;
- Develop software as a modular framework so that single components can be updated without requiring re-work on other pieces;
- Build a secure and verifiable update mechanism into the device;
- Follow system-hardening procedures for IoT devices (disable extraneous services, etc.);
- Respond favorably to reports of vulnerabilities and work with, instead of against, reporting individuals to rectify the problem.
IoT is steadily creeping into every nook and cranny of our lives, from our workplaces to our bedrooms. Unless we address the security problem now, it could boil over into something that would be extremely costly to remediate.
