Armor, leading cloud security solutions provider and publisher of the annual Black Market Report is warning computer users and e-commerce retailers to be on the lookout for malicious phishing campaigns and Magecart attacks this holiday season.
According to Armor’s intelligence sources, a malicious phishing campaign or campaigns is expected to launch on or around December 1 and run through December 25, 2018. The subject of the phishing emails is expected to be about an online order or shipping notification, and the “Sent From” address will appear as if the emails are coming from a popular e-commerce retailer or a package delivery organization, e.g. Amazon, UPS, FedEx, USPS, etc.
The fake emails are expected to look very authentic and crafted so as to illicit an immediate response from the recipient, most likely enticing them to click on a malicious link or attachment which potentially leads to a banking trojan, ransomware or keylogger.
On November 26 Armor’s security team, the Threat Resistance Unit (TRU) detected and analyzed a well-crafted, phishing email purporting to be from Amazon and said to contain a $500 credit for Cyber Monday . See Image 1. Upon analysis, Armor found that the email was not sent from Amazon but rather was sourcing out of Chile from an open-source email service, and the enclosed $500 credit coupon links to a separate non-Amazon domain which has been reported to be malicious, according to Trend AV and other AV vendors, and is reported to be a part of an Emotet banking trojan distribution campaign.

Image 1—a November 26, 2018 phishing email, purporting to be from Amazon, but in actuality is reported to a part of the Emotet banking trojan distribution campaign.
On November 30, the TRU team saw reports of an almost identical phishing email being sent to online shoppers in the U.K. These phishing emails included an enticing £500 pound Amazon credit, and the offer was valid from November 26 through November 30, and the threat actors updated the “From” address to make it appear as if it was coming from: cybermonday@amazon.com.uk. . See Image 2. These emails also appear to be part of the Emotet Banking Trojan malware distribution campaign.
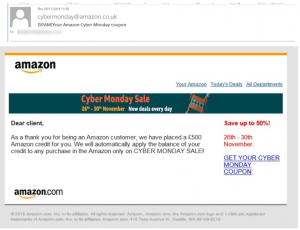
Image 2—a phishing email, almost identical to the phishing email in Image 1 being distributed the week of November 26 and customized for UK online shoppers . This email is also reported to be a part of the Emotet banking trojan distribution campaign.
And although the U.S. and U.K. phishing emails had end dates the week of November 30, the TRU Team is confident that the threat group behind this Emotet distribution scheme will extend the credit expiration dates in the lure so as to take advantage of the entire holiday shopping season.
These “Amazon “spoofed” phishing emails are not a part of the campaign expected to launch on or around December 1, however, they do contain many of the attributes Armor expects to see in the forthcoming emails, including:
- Spoofing a major brand in both the “From” address and the body of the email
- Using logos and other graphics, which mimic those used by the brand being spoofed (these emails included Amazon-looking logos throughout the emails and including an Amazon-looking copyright notice).
- Include an immediate call to action in the email so as to entice the recipient to click on the enclosed link or attachment (these emails included an offer of $500 USD/pounds credit which was due to expire soon, making it very alluring. One can see where it would be easy for an online user to fall for these phishing email).
Corey Milligan, sr. security researcher with the TRU Team stated, “These types of malicious campaigns happen every year and throughout the calendar year. However, they become more prevalent during the holiday season when online shopping is at its height. What I found particularly interesting about this security alert is that it specifically named the dates in which this malicious campaign was to run, December 1 through December 25, and we don’t usually see such specificity when getting these threat alerts. Therefore, computer users need to be especially vigilant during the holidays because the threat actors are intent on stealing as much credit card, banking and personal identifiable information as they can get their hands. This data can translate into a lot of money for them.” Therefore, the TRU Team recommends computer users and mobile users consider adopting the following security precautions, not just during the holidays but all year long.
- Keep your software up-to-date. Unpatched operating systems, applications, browsers, and browser plugins are often just the weaknesses threat actors are looking for. Keeping them up-to-date with the latest security patches along with using an up-to-date anti-virus program should be thought of as minimum security precautions.
- Avoid using “free” wireless access, VPNs and proxy services. Free services are tempting but should always be viewed as a risk as nothing is truly free. When you connect to a device/service that routes/redirects your traffic, you are voluntarily connecting to a man-in-the-middle, allowing a third- party to see everything you are doing over that connection. In the case of online shopping, this means that they are at least seeing the sites you are shopping on, and at worst they could be collecting your payment information or redirecting you to malicious sites. ALWAYS use a trusted network when shopping online or performing ANY financial transactions.
- When making online purchases, look for HTTPS (locked padlock) in the address bar. This is a good practice as seeing this means that your connection to a site is encrypted. However, it doesn’t mean the site should be trusted completely, as many threat actors are leveraging HTTPS sites with valid certificates in their attacks.
- DO NOT click on links or attachments in emails, social media feeds or websites, even if you know the sender. One should especially be wary of holiday gift cards, coupons, photos and holiday greeting cards. It’s always a good idea to verify with the sender that they sent you the email with the enclosed link or attachment. However, beyond that, attachments should always be scanned with an anti-virus program before opening. With the prevalence of attacks that are launched through email, it’s worth taking the extra time to examine the contents of a link to ensure it is taking you to the site you expect it to, and paste/type it into a browser rather than clicking on a link.
- Make online purchases using a credit card rather than a debit card, or better yet, use a prepaid card.While most banks offer services to help you recover from fraud, it can take time. In the case of a debit card, the time it takes to recover stolen funds that may be needed to pay a bill is too big of a risk to take. Using a credit card reduces this risk, but an even better solution is to use a prepaid card. Prepaid cards are easy to obtain, even for those with no credit history, and they limit the amount that can be stolen via fraud to the amount of money you put on the card. Prepaid cards may not be the most convenient or cost-effective solution, but they can help keep your credit and bank account information out of the hands of criminals.
- Do NOT respond to unsolicited/unverified emails, especially those from a bank or financial institution asking for account or personal information. Most online service providers and financial institutions will not ask customers to update information via email, and they never ask you to disclose sensitive information via email.
- Avoid using weak or default passwords for any online site.Use a different password for each site; store your passwords securely; and auto-generate new, strong passwords with a passport management tool such as LastPass or Ke ePass.
- If possible, use a computer dedicated solely for accessing financial accounts, online purchases and paying bills. This computer should not be used for surfing the Internet or for emailing, the primary vectors for infecting your computer. This computer should also be used on a trusted network.
- Consumers should consider freezing their credit.
It is the Most Wonderful Time of the Year for Harvesting Credit Card Data
With the recent rush of reporting around the Magecart threat group and their associated attacks, the TRU Team expects that Magecart-style breaches will be the soup du jour of the holiday season. They believe that Magecart threat actors will use the holiday rush to gather as much credit card data as they can before cyber defenders can figure out how to put a stop to their Techniques, Tactics and Procedures (TTPs). Additionally, the TRU team expects instances of low sophistication Magecart copycats to increase, so as to take advantage of the holiday frenzy and the current success of the Magecart- style attacks.
What is Magecart?
As far back as 2015, intelligence organizations and security researchers, such as RiskIQ and Willem DeGroot, have been tracking and reporting about a growing trend and associated techniques for what is now being termed online credit card skimming. Magecart draws its name from its original TTP discovery in which Magento content management system (CMS) instances, with shopping cart functionality, were being scanned for, targeted and attacked. Thus, you have ‘Mage’nto shopping ‘cart’, or Magecart. In this initial TTP, a vulnerability in a Magento site was leveraged to modify the source code of the site, injecting what looked like a legitimate download of a JavaScript library. In actuality, when a browser would connect to the site, it would automatically download this JavaScript file, as is common, and run it in the browser. The malware would identify the shopping cart functionality and modify it so that a copy of any credit card information that was submitted would be sent to a server owned by the threat actor.
Although the Magecart name continues to be used, online card skimming attacks have evolved beyond targeting only Magento sites. At least six separate groups have been identified to be using a similar TTP of modifying e-commerce sites with malicious JavaScript files. The unique qualities that allow these threat actors to be singled out include variances in sophistication and target selection with the most high-profile breaches being those that have leveraged the software supply chain (Inbenta, Feedify and Shopper Approved) and those that have targeted specific high-traffic sites (British Airways and Newegg).
How Can E-Commerce Retailers Protect Themselves and their Customers from Magecart Attacks?
While these recommendations are ranked, Good, Better, Best, it is recommended that, where possible, these techniques are used in combination with each other to provide a layered defense.
Good
– Keep your payment page simple. Loading third-party scripts along with your payment processing page increases your risk of third-party compromise. Many third-party content providers are not focused on security. Threat actors are known to choose the softer target ,and they will not hesitate to circumvent your security by compromising a third-party you are trusting on your payment processing page.
Better
– Audit public facing web content regularly to identify unauthorized changes.
– Use subresource integrity for embedded scripts. On its own, it won’t protect you from all forms of third-party code injection attacks, but as a practice it raises your level of security and makes you a harder target.
– As a backup measure and a step to mitigate similar attacks, a content security policy (CSP) header can be employed. This additional header for web content tells the browser, that is accessing your site, where resources are authorized to be downloaded from. While this won’t stop the download of scripts from compromised, trusted third-parties, it does help mitigate other HTML injection attacks where the content source has been changed to an untrusted download source.
Best
– Outsource your payment processing to a third-party payment processor. While this involves trusting a third-party, all third-parties are not equal. Of course, do your homework before selecting one, but, in general, payment processors that perform this service have well implemented security practices. While there will be additional costs involved with using an external payment processor, it can also relieve you of many stringent PCI requirements that have costs of their own to maintain.
After-the-fact
If you have been affected by one of these type attacks, and the third-party code supplier has taken steps to clean it up, you may still be vulnerable if you are using a Content Delivery Network (CDN) that caches content to improve performance. If this is the case, be sure to flush cached pages as one of the final steps to cleanup.
How Online Shoppers Can Protect Themselves from a Magecart Attack?
As an online shopper, to protect your payment card details safe from a Magecart attack, disable JavaScript inside your browser before making a payment. Since the card skimming code is written in JavaScript, this will prevent a standard Magecart attack. (NOTE: disabling JavaScript in your browser may also cause webpages not to function. In the case that you need to leave JavaScript enabled, see our recommendation about using prepaid cards for online purchases).
What is Your Credit Card, Bank Account or Personal Identity Worth on the Underground Hacker Markets?
Prices for Stolen Credit Card Data on the Underground
So, you don’t think that hackers are interested in your online bank account credentials, credit card, or personally identifiable information (PII)? Well, think again. Armor’s (TRU) team recently did a deep dive into prices for these items looking at dozens of Underground Hacker Markets and finding that a buyer can purchase basic credit card data, for anywhere from $9 to $26, depending on the country of origin and the type of credit card. The prices go up for credit card data with corresponding CVV codes, starting at $15 a piece and they really go up in price when the card data contains personally-identifiable information of the cardholder (name, address, age, phone, social security number or national identifying number, email address and mother’s maiden name) enabling the fraudsters to circumvent fraud questions implemented by the merchants. These credit cards usually have balance limits starting at $3,000 going up to $50,000 and will range in price from $65 to $75, depending on the card type and the country of origin.
Prices of Online Bank Account Credentials on the Underground
The prices for online bank account credentials currently range from an average of $269 up to $1,200 depending on the country location of the account and the balance of the account.
Prices for Full Identities (Fullz) on the Underground
The TRU team also looked at the prices of Fullz, which is a packet of Personally identifiable information (PII). These full identities typically include:
First name
Last name
Current Home/Billing Address
Previous Home/Billing address
City
State
Zip
Country
Mobile and/ or home phone
Work phone
SSN or National Identity Number
Date of Birth
Mother’s Maiden Name
Credit card number
The prices for a Full Identity package or Fullz runs between $24 and $57 depending on the victim’s country of origin. The TRU team observed several cybercriminals who also offered to sell additional data, relating to a victim, if the buyer was willing to pay a bit more money. This information included such items as an individual’s bank account type, bank account number, bank routing number, bank security questions and answers, driver’s license number, and victim’s employer.
Conclusion
The holiday season should be a magical time spent enjoying friends and loved ones. However, not everyone online is full of well wishes. As the past years have shown, there is no end to the online crime schemes threat actors are able to devise, such as the very ingenious Magecart attacks or the countless holiday cyber scams. And with online shopping continuing to grow, resulting in record online sales, the TRU team is confident that this holiday season will see more Magecart- style attacks(online card skimming attacks) and more malicious phishing campaigns. With the seemingly endless supply of spam botnets available for hire, one can count on plenty of emails circulating containing poisonous attachments or links, disguised as package delivery notifications, online order confirmations, holiday coupons and gift cards, e-greeting cards and holiday photos. Thus, this holiday season and throughout the year, the TRU team hopes that all computer users and e-commerce retailers will stay alert, stay vigilant and follow the security precautions outlined so as to ensure that everyone experiences an enjoyable holiday and new year.